Manufacturing Cybersecurity: Protecting Industrial Automation Systems

Manufacturing Cybersecurity: Protecting Industrial Automation from Emerging Threats
Manufacturing now faces the highest rate of cyberattacks across all industries. Recent data shows over 25% of incidents target this sector. Digital transformation expands the attack surface dramatically. Companies must prepare for when attacks occur, not if they will happen.
The Current Manufacturing Threat Landscape
Ransomware dominates manufacturing cyber incidents at 68%. Business email compromise follows closely behind. Account takeovers and web attacks are also increasing. Insider threats targeting intellectual property remain a serious concern. These attacks cause widespread operational disruption.
Real-World Attack Consequences
Cyber incidents create massive financial losses and production halts. One manufacturer lost $85 million in a 2023 breach. Operations stopped for over a week in several cases. Supply chain disruptions and reputational damage often follow. Stock prices can drop significantly after public disclosure.
Major Manufacturing Cyber Incidents
- Clorox experienced unauthorized IT access in 2023. Multiple manufacturing sites faced operational disruptions. The company reported substantial financial impacts.
- Varta disconnected systems after a 2024 cyber incident. Production halted for two weeks during recovery. Containment efforts required complete isolation.
- Halliburton suffered ransomware from RansomHub group. Billing and purchase order processing failed. Losses reached $35 million with 10% stock decline.
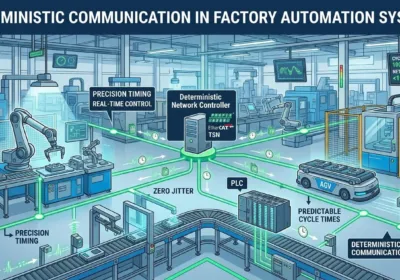
Industrial Automation Security Challenges
Manufacturers face unique cybersecurity obstacles. Legacy control systems lack modern security features. IT/OT convergence creates new vulnerability points. Third-party vendors introduce additional risk vectors. Talent shortages complicate security management.
Essential Protection Strategies
Proactive security measures significantly reduce risk. Regular vulnerability assessments identify weaknesses early. Network segmentation contains potential breaches. Comprehensive employee training prevents social engineering attacks. Strong access controls protect critical assets.
Technical Security Implementation
- Implement network segmentation for PLC and DCS systems
- Conduct regular penetration testing on control systems
- Apply privileged access management to automation networks
- Develop incident response plans for factory automation
- Install continuous monitoring for industrial control systems
- Maintain updated disaster recovery procedures
Compliance and Standards Framework
ISA/IEC 62443 provides crucial guidance for industrial security. GDPR compliance ensures data protection standards. SOC II certification demonstrates security commitment. Insurance providers increasingly require these frameworks. Compliance reduces liability and improves insurability.
Effective Tabletop Exercises
Simulated incidents prepare teams for real attacks. Exercises define clear roles and responsibilities. They validate communication and recovery assumptions. Organizations identify policy gaps proactively. Leadership sees security investment value demonstrated.
PLCDCSHUB Security Recommendations
At PLCDCSHUB, we recommend layered security for industrial automation. Start with comprehensive risk assessment for all control systems. Implement network segmentation between IT and OT environments. Regular security audits for PLC and DCS systems are essential. According to IBM’s 2024 report, manufacturing attacks increased 45% year-over-year. We suggest integrating industrial automation security into business continuity planning.
Practical Implementation Scenario
Consider an automotive parts manufacturer with legacy equipment. They implement network segmentation for their production lines. Regular vulnerability scanning identifies PLC security gaps. Employee training reduces phishing success rates. Incident response testing ensures quick recovery. These measures significantly reduce cyber risk.
Frequently Asked Questions
- Why are manufacturers targeted by cyberattacks? Manufacturing systems often run critical operations with legacy equipment, making them attractive targets for disruption and ransom.
- How can we secure older industrial control systems? Implement network segmentation, access controls, and monitoring while planning for gradual system upgrades.
- What makes tabletop exercises valuable? They reveal response gaps and improve team coordination without risking actual operations.